I am looking help for ASP.NET MVC application. Which authenticate single tenant azure active directory users and can authorize users using active directory security group. i.e. if user is part of that security group then only allow access to website otherwise access denied.
Active directory authentication can be done by visual studio itself using wizard but not sure how to perform authorization through AAD security group.
P.S. I am new to ASP.NET security
Answers:
Thank you for visiting the Q&A section on Magenaut. Please note that all the answers may not help you solve the issue immediately. So please treat them as advisements. If you found the post helpful (or not), leave a comment & I’ll get back to you as soon as possible.
Method 1
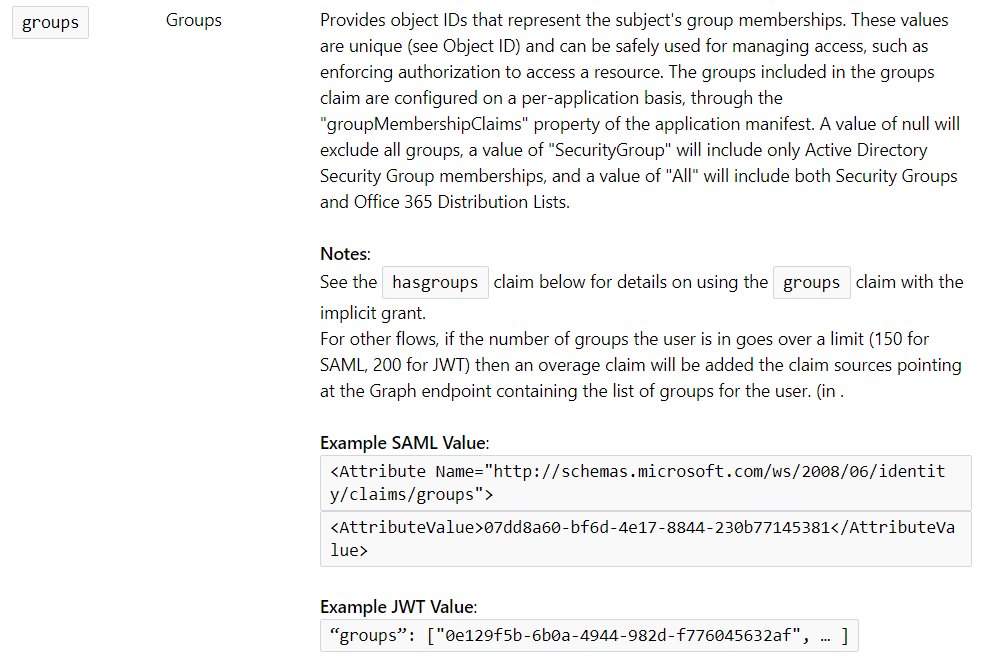
When a user signs into the application, incoming token from Azure AD will contain group claims, once you modify the application’s manifest appropriately (see the sample application link below for steps). Your application code can then read these claims and make authorization decisions based on them.
Here is a sample application that does authorization based on group claims –
Authorization in a web app using Azure AD groups & group claims
ADDITIONAL INFORMATION TO CONSIDER WHEN IMPLEMENTING AUTHORIZATION LOGIC
-
You have specifically asked about Groups, but you should also consider using Application Roles, which can help you implement a Role based authorization logic. Look at Microsoft documentation link Application Roles. Here is a link to another similar question where I have provided a little more detailed information on both Application Roles and Groups and links to sample code for both.
Azure Active Directory Integration with Custom RBACOnce you understand the usage/purpose of application roles and groups, it’s completely possible for you to decide that you want to base your authorization logic on a combination of Roles and Groups information for the signed in user instead of just one.
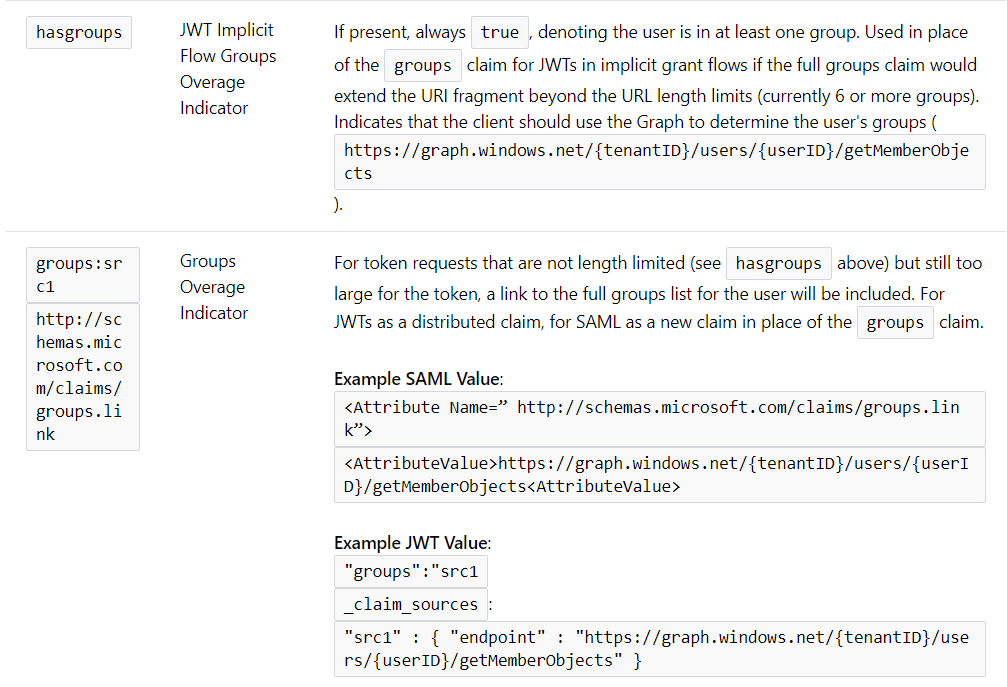
- In case when a user is part of many groups (6 or more AFAIK), Azure AD token doesn’t send across the “groups” directly as part of token, instead it sends an overage indicator and then you can query the groups in a separate call. Take a look at the token related documentation here – Claims in id_tokens
All methods was sourced from stackoverflow.com or stackexchange.com, is licensed under cc by-sa 2.5, cc by-sa 3.0 and cc by-sa 4.0