Related question: initiate ssh connection from server to client
Answer from there helped me a lot, this command does what I need:
ssh -R 2225:localhost:22 <a href="https://getridbug.com/cdn-cgi/l/email-protection" class="__cf_email__" data-cfemail="3d51525a5453725b6e584f4b584f6a5449556d485f51545e746d7d4d485f51545e746d">[email protected]</a>
So I wrote the script to reconnect all the time:
#!/bin/bash
while true; do
echo "try to connect..."
ssh -o ServerAliveInterval=240 -R 2225:localhost:22 <a href="https://getridbug.com/cdn-cgi/l/email-protection" class="__cf_email__" data-cfemail="0376706671436b6c7077">[email protected]</a>
echo "restarting in 5 seconds.."
sleep 5
done
And added it to the /etc/crontab. But I found out that works if only I execute it “by hand” from shell, but if it is called by cron, ssh connects and immediately finishes. (so, the script above reconnects all the time)
From man ssh, I found that for background connections I should call it with -n key, but it didn’t help. Then, I just looked around for similar scripts and I found that it works if I call tail -f something, i.e. some “neverending” command, so I just created empty file /tmp/dummy_file and now my ssh command looks like this:
ssh -o ServerAliveInterval=240 -R 2225:localhost:22 -n <a href="https://getridbug.com/cdn-cgi/l/email-protection" class="__cf_email__" data-cfemail="c6b3b5a3b486aea9b5b2">[email protected]</a> tail -f /tmp/dummy_file
It works now! But, this solution seems a bit ugly, plus I don’t really understand actual reasons of that behavior. Just by chance, I tried to call bash instead of tail -f (bash seems to me “neverending” command, too), but it doesn’t work.
So, could anyone please explain this behavior, and what is the correct way to create background ssh connection to keep reverse ssh tunnel up?
Answers:
Thank you for visiting the Q&A section on Magenaut. Please note that all the answers may not help you solve the issue immediately. So please treat them as advisements. If you found the post helpful (or not), leave a comment & I’ll get back to you as soon as possible.
Method 1
It sounds like you want the -N option to ssh.
-N Do not execute a remote command. This is useful for just forwarding ports
(protocol version 2 only).
Method 2
I would strongly suggest you consider autossh. It has certain heuristics that will allow it to determine if connection loss is the underlying reason and will lower the frequency of reconnection attempts. In addition it monitors the connection using extra tunnels, which makes it highly useful for scenarios like the one you are asking about.
If you are on Ubuntu, for example, you can do a web search for autossh upstart to find some useful examples on how to configure Ubuntu so that the tunnel is kept up in a persistent fashion.
I am using this to keep a tunneled connection open to my server at all times for certain services.
Method 3
I’ll second @0xC0000022L’s suggestion and use autossh as well. I use it to maintain a SSH connection from my laptop as I take it from place to place and it just works. I use this connection to tunnel back ports 25 and 2143 for access to my personal SMTP and IMAP servers.
Here’s the script that I use:
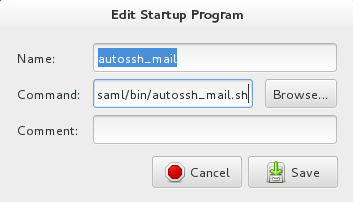
$ more /home/saml/bin/autossh_mail.sh #!/bin/bash autossh -M 0 -f -N -L 2025:localhost:25 -L 2143:localhost:143 <a href="https://getridbug.com/cdn-cgi/l/email-protection" class="__cf_email__" data-cfemail="86f5e7ebc6efebe7f6abe9">[email protected]</a>
I then maintain a Host entry in my $HOME/.ssh/config file for host imap-o.
$ more $HOME/.ssh/config
ServerAliveInterval 15
ForwardX11 yes
ForwardAgent yes
ForwardX11Trusted yes
GatewayPorts yes
Host *
ControlMaster auto
ControlPath ~/.ssh/master-%<a href="https://getridbug.com/cdn-cgi/l/email-protection" class="__cf_email__" data-cfemail="255765">[email protected]</a>%h:%p
IdentityFile ~/.ssh/id_dsa
Host imap-o
User sam
ProxyCommand ssh <a href="https://getridbug.com/cdn-cgi/l/email-protection" class="__cf_email__" data-cfemail="3340525e735e4a54441d5e4a575c5e1d505c5e">[email protected]</a> nc `echo %h|sed 's/-o//'` %p
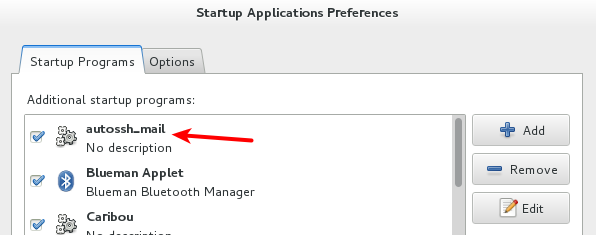
The autossh_mail.sh script is run as part of my desktop when I log in. You can access it via gnome-session-properties.
All methods was sourced from stackoverflow.com or stackexchange.com, is licensed under cc by-sa 2.5, cc by-sa 3.0 and cc by-sa 4.0